#rsETHAttackUpdate : Technical Analysis of DeFi's Largest Cross-Chain Attack
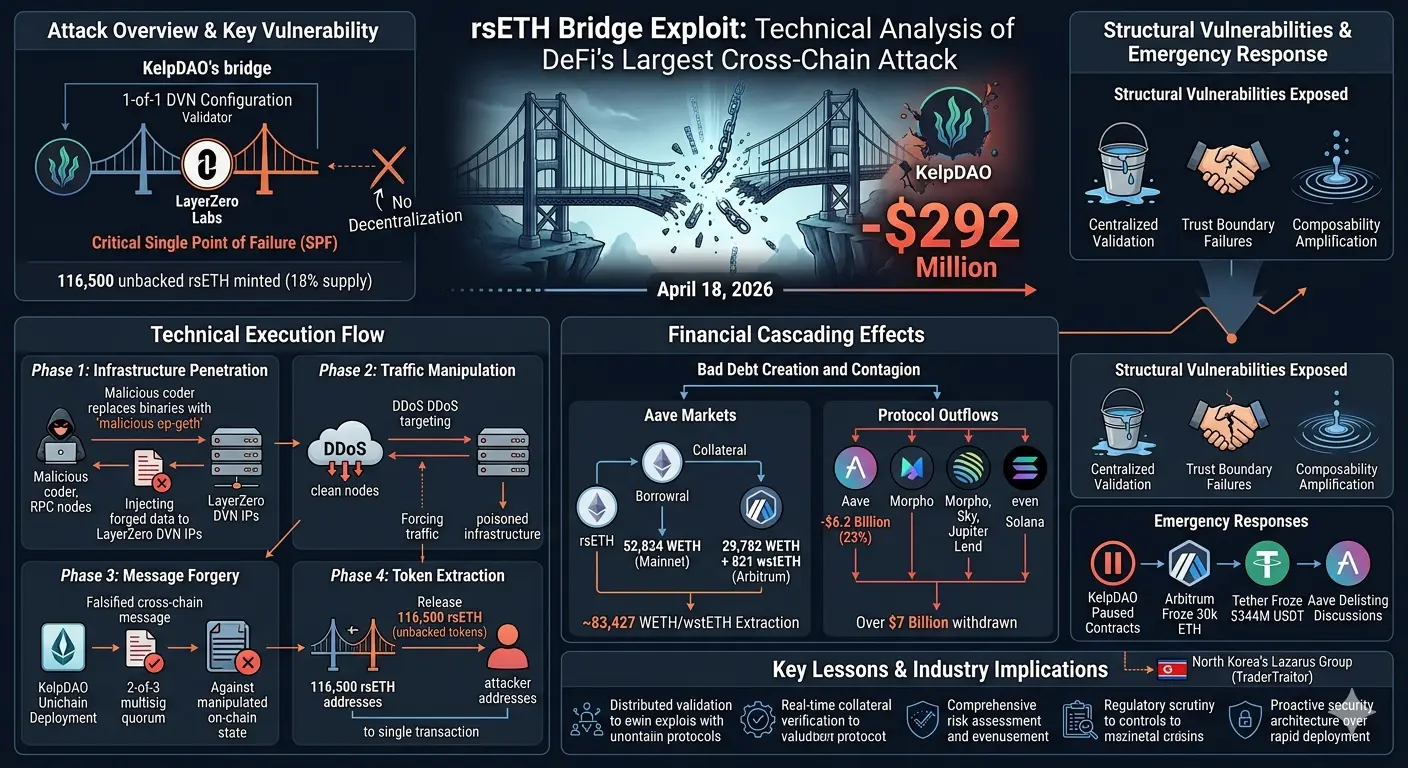
On April18,2026, KelpDAO's rsETH protocol suffered a $292 million exploit through its LayerZero bridge, marking one of DeFi's most significant security failures. This briefing examines the attack vectors, cascading effects, and structural vulnerabilities exposed.
Attack Overview
The attacker minted116,500 unbacked rsETH tokens (18% of total supply) by compromising KelpDAO's cross-chain infrastructure. The exploit targeted a critical architectural weakness: KelpDAO's bridge operated with a1-of-1 DVN (Decentralized Validator Network) configuration, making LayerZero Labs the sole verification entity for cross-chain messages.
Technical Execution
The attack followed a sophisticated multi-phase approach:
1. Infrastructure Penetration: Attackers gained access to RPC nodes used by the LayerZero DVN, replacing legitimate op-geth binaries with malicious versions that served forged data exclusively to the DVN's IP addresses.
2. Traffic Manipulation: Through DDoS attacks on clean nodes, attackers forced complete failover to compromised infrastructure, ensuring all verification traffic routed through poisoned endpoints.
3. Message Forgery: A fabricated cross-chain message claiming origin from KelpDAO's Unichain deployment was validated against manipulated on-chain state, passing the2-of-3 multisig quorum.
4. Token Extraction: The bridge released116,500 rsETH to attacker-controlled addresses in a single transaction, creating unbacked tokens with no underlying collateral.
Attribution analysis points to North Korea's Lazarus Group (TraderTraitor), known for advanced cryptocurrency exploits targeting financial infrastructure.
Financial Cascading Effects
The attacker immediately deployed unbacked rsETH as collateral across Aave V3 and V4 markets:
- Borrowed52,834 WETH on Ethereum mainnet
- Borrowed29,782 WETH plus821 wstETH on Arbitrum
- Total extraction: approximately83,427 WETH and wstETHThis created substantial bad debt within Aave's lending markets. The protocol responded within hours by freezing rsETH markets and removing borrowing power, but damage extended across DeFi:
- Over $7 billion withdrawn from leading protocols
- Aave lost $6.2 billion (23% of TVL)
- Similar outflows hit Morpho, Sky, and Jupiter Lend
- Panic withdrawals affected even unaffected protocols on Solana Emergency Responses
Multiple protocols and networks implemented damage control measures:
- KelpDAO paused rsETH contracts across mainnet and L2s
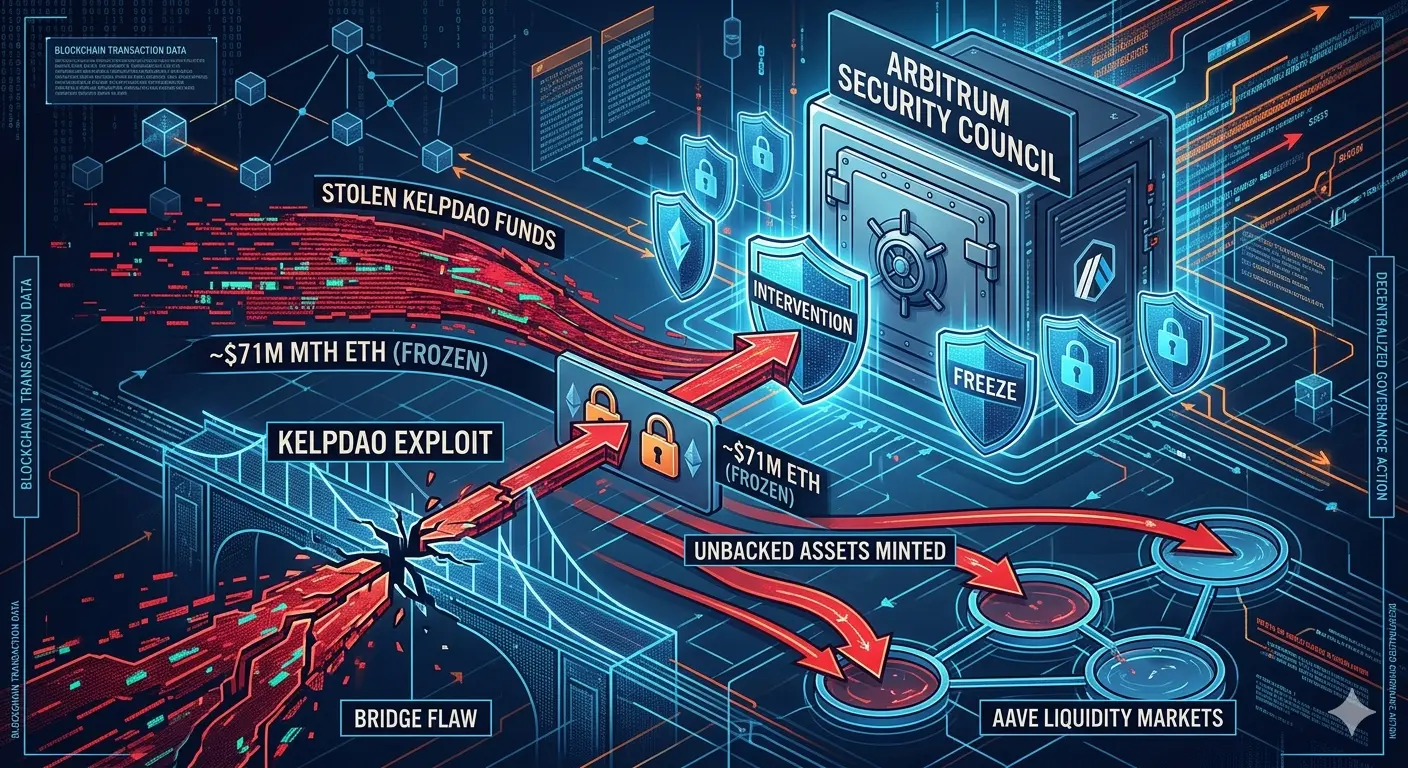
- Arbitrum froze30,000 ETH ($71 million) linked to exploit addresses
- Tether froze $344 million USDT across two Tron wallets
- Aave community initiated discussions on permanent rsETH delisting Structural Vulnerabilities Exposed
The exploit reveals fundamental weaknesses in DeFi's cross-chain architecture:
Centralized Validation: Despite decentralization marketing, bridges often rely on concentrated verification. The1-of-1 DVN configuration created a catastrophic single point of failure.
Trust Boundary Failures: The exploit occurred at LayerZero's message verification and KelpDAO's bridge acceptance intersection, demonstrating how modular security without robust standards creates systemic risk.
Composability Amplification: Attackers leveraged unbacked tokens across multiple protocols, showing how DeFi's interconnected nature magnifies individual failures.
Governance Reality Gap: DeFi operates where theoretical decentralization masks practical control concentration, complicating accountability and emergency response.
Industry Implications
This incident carries significant consequences for DeFi development:
Security Standards: Cross-chain bridges require distributed validation mechanisms and elimination of single points of failure. The industry must establish minimum security standards for bridge architecture.
Risk Assessment: Lending protocols need real-time collateral verification and stricter assessment of bridged asset backing before accepting deposits.
Emergency Protocols: Rapid market freezing capabilities are essential, but reactive measures cannot substitute for preventive security architecture.
Regulatory Scrutiny: Exploits of this scale accelerate regulatory attention and compliance pressure on DeFi protocols.
Accounting Challenges: Auditors face fundamental difficulties evaluating control effectiveness when validation relies on potentially compromised off-chain infrastructure.
Key Lessons
For developers and participants:
1. Bridge security architecture demands multi-signature distributed validation, not single-entity verification.
2. Collateral backing must be verifiable in real-time, particularly for cross-chain assets.
3. Protocol composability creates systemic risk requiring comprehensive security assessment.
4. Emergency response capabilities must be balanced with preventive security measures.
5. Due diligence on underlying infrastructure security is essential before depositing funds.
Conclusion
The rsETH exploit demonstrates that in DeFi, bridge design inseparably determines asset security. Distribution across chains does not distribute risk automatically. This incident exposes the tension between rapid scalability and robust security architecture that defines DeFi's current evolution.
The attack reveals a fundamental truth: decentralized governance in theory often masks concentrated control in practice. For DeFi to achieve resilient financial infrastructure, the industry must address these architectural vulnerabilities through stronger standards, distributed validation mechanisms, and protocols prioritizing security over deployment speed.
The cascading effects across Aave and other protocols show how quickly individual bridge failures become systemic crises. As DeFi matures, cross-chain security must evolve from an afterthought to a foundational design principle.
Preliminary attribution to state-sponsored actors adds geopolitical dimension to DeFi security challenges. The sophistication demonstrated suggests future attacks may increase in complexity and impact, making proactive security investment essential for protocol survival.
This incident will likely accelerate development of more resilient cross-chain solutions while prompting comprehensive reassessment of bridge-related risk exposure across the DeFi ecosystem. The question is no longer whether bridges can be secured, but whether the industry can implement adequate security standards before the next exploit occurs.
#rsETHExploit #DeFiSecurity #CrossChainRisk #KelpDAOHack
On April18,2026, KelpDAO's rsETH protocol suffered a $292 million exploit through its LayerZero bridge, marking one of DeFi's most significant security failures. This briefing examines the attack vectors, cascading effects, and structural vulnerabilities exposed.
Attack Overview
The attacker minted116,500 unbacked rsETH tokens (18% of total supply) by compromising KelpDAO's cross-chain infrastructure. The exploit targeted a critical architectural weakness: KelpDAO's bridge operated with a1-of-1 DVN (Decentralized Validator Network) configuration, making LayerZero Labs the sole verification entity for cross-chain messages.
Technical Execution
The attack followed a sophisticated multi-phase approach:
1. Infrastructure Penetration: Attackers gained access to RPC nodes used by the LayerZero DVN, replacing legitimate op-geth binaries with malicious versions that served forged data exclusively to the DVN's IP addresses.
2. Traffic Manipulation: Through DDoS attacks on clean nodes, attackers forced complete failover to compromised infrastructure, ensuring all verification traffic routed through poisoned endpoints.
3. Message Forgery: A fabricated cross-chain message claiming origin from KelpDAO's Unichain deployment was validated against manipulated on-chain state, passing the2-of-3 multisig quorum.
4. Token Extraction: The bridge released116,500 rsETH to attacker-controlled addresses in a single transaction, creating unbacked tokens with no underlying collateral.
Attribution analysis points to North Korea's Lazarus Group (TraderTraitor), known for advanced cryptocurrency exploits targeting financial infrastructure.
Financial Cascading Effects
The attacker immediately deployed unbacked rsETH as collateral across Aave V3 and V4 markets:
- Borrowed52,834 WETH on Ethereum mainnet
- Borrowed29,782 WETH plus821 wstETH on Arbitrum
- Total extraction: approximately83,427 WETH and wstETHThis created substantial bad debt within Aave's lending markets. The protocol responded within hours by freezing rsETH markets and removing borrowing power, but damage extended across DeFi:
- Over $7 billion withdrawn from leading protocols
- Aave lost $6.2 billion (23% of TVL)
- Similar outflows hit Morpho, Sky, and Jupiter Lend
- Panic withdrawals affected even unaffected protocols on Solana Emergency Responses
Multiple protocols and networks implemented damage control measures:
- KelpDAO paused rsETH contracts across mainnet and L2s
- Arbitrum froze30,000 ETH ($71 million) linked to exploit addresses
- Tether froze $344 million USDT across two Tron wallets
- Aave community initiated discussions on permanent rsETH delisting Structural Vulnerabilities Exposed
The exploit reveals fundamental weaknesses in DeFi's cross-chain architecture:
Centralized Validation: Despite decentralization marketing, bridges often rely on concentrated verification. The1-of-1 DVN configuration created a catastrophic single point of failure.
Trust Boundary Failures: The exploit occurred at LayerZero's message verification and KelpDAO's bridge acceptance intersection, demonstrating how modular security without robust standards creates systemic risk.
Composability Amplification: Attackers leveraged unbacked tokens across multiple protocols, showing how DeFi's interconnected nature magnifies individual failures.
Governance Reality Gap: DeFi operates where theoretical decentralization masks practical control concentration, complicating accountability and emergency response.
Industry Implications
This incident carries significant consequences for DeFi development:
Security Standards: Cross-chain bridges require distributed validation mechanisms and elimination of single points of failure. The industry must establish minimum security standards for bridge architecture.
Risk Assessment: Lending protocols need real-time collateral verification and stricter assessment of bridged asset backing before accepting deposits.
Emergency Protocols: Rapid market freezing capabilities are essential, but reactive measures cannot substitute for preventive security architecture.
Regulatory Scrutiny: Exploits of this scale accelerate regulatory attention and compliance pressure on DeFi protocols.
Accounting Challenges: Auditors face fundamental difficulties evaluating control effectiveness when validation relies on potentially compromised off-chain infrastructure.
Key Lessons
For developers and participants:
1. Bridge security architecture demands multi-signature distributed validation, not single-entity verification.
2. Collateral backing must be verifiable in real-time, particularly for cross-chain assets.
3. Protocol composability creates systemic risk requiring comprehensive security assessment.
4. Emergency response capabilities must be balanced with preventive security measures.
5. Due diligence on underlying infrastructure security is essential before depositing funds.
Conclusion
The rsETH exploit demonstrates that in DeFi, bridge design inseparably determines asset security. Distribution across chains does not distribute risk automatically. This incident exposes the tension between rapid scalability and robust security architecture that defines DeFi's current evolution.
The attack reveals a fundamental truth: decentralized governance in theory often masks concentrated control in practice. For DeFi to achieve resilient financial infrastructure, the industry must address these architectural vulnerabilities through stronger standards, distributed validation mechanisms, and protocols prioritizing security over deployment speed.
The cascading effects across Aave and other protocols show how quickly individual bridge failures become systemic crises. As DeFi matures, cross-chain security must evolve from an afterthought to a foundational design principle.
Preliminary attribution to state-sponsored actors adds geopolitical dimension to DeFi security challenges. The sophistication demonstrated suggests future attacks may increase in complexity and impact, making proactive security investment essential for protocol survival.
This incident will likely accelerate development of more resilient cross-chain solutions while prompting comprehensive reassessment of bridge-related risk exposure across the DeFi ecosystem. The question is no longer whether bridges can be secured, but whether the industry can implement adequate security standards before the next exploit occurs.
#rsETHExploit #DeFiSecurity #CrossChainRisk #KelpDAOHack